AI in operations is no longer a future-state idea. For most engineering teams, it is quickly becoming the difference between controlled incidents and noisy firefights. The goal is not replacing on-call engineers. The goal is giving them cleaner context, faster hypotheses, and better handoff quality.
This guide focuses on the workflows that matter this week: incident summarization, prioritization, runbook automation, and release risk scoring. Every section includes concrete steps you can test in production-safe ways.
What AI for DevOps Means in Practice
Quick Answer: AI for DevOps is the use of machine learning systems inside delivery and reliability loops so engineers can move from raw alerts to concrete actions faster.
AI for DevOps sounds abstract until you map it to the exact work developers already do. Think of it like adding a skilled dispatcher in a crowded emergency room: the doctors still make the final call, but triage gets sharper, context arrives faster, and fewer critical patients wait in the hallway. In engineering terms, that means incidents, deploy signals, and telemetry are pre-processed into ranked, explainable tasks before they hit your on-call channel.
In this article, DevOps (development and operations) means the practice of shipping code and operating systems as one continuous loop, while SRE (Site Reliability Engineering) means the discipline of enforcing reliability through measurable service objectives. According to the Google SRE Workbook, reliability programs perform best when error budgets and operational policies are explicit rather than implicit. That makes AI useful only when it respects those policies and surfaces risk with enough evidence that a human can verify the recommendation quickly.
Use this definitions block as your baseline language before tooling decisions:
- Incident summarization: a model-generated timeline that compresses logs, alerts, and deploy changes into a readable sequence.
- RCA (root cause analysis): the process of identifying the underlying technical trigger instead of the first visible symptom.
- Runbook generation: turning repeated remediation steps into structured, reusable procedures.
- Alert deduplication: merging noisy, near-identical alerts into a single actionable incident card.
- Change risk scoring: estimating release risk by combining code churn, dependency drift, and historical failure data.
- Post-incident learning loop: feeding lessons from retrospectives back into monitors, tests, and runbooks.
| Technical Requirement | Potential Risk | Learner's First Step |
|---|---|---|
| Unified telemetry pipeline | AI sees fragmented events and hallucinates causality | Standardize logs, metrics, and traces through one ingestion path |
| Service ownership map | Recommendations are accurate but unassignable | Add owner metadata to services and alert policies |
| Runbook metadata | Suggested fixes cannot be verified during incidents | Tag every runbook with preconditions and rollback criteria |
To connect this workflow with your existing stack, link the rollout to the pillar guide, AI debugging workflows, AI code review controls, model behavior mechanics, and prompt templates for developers. That internal map keeps teams from treating each article as an isolated tactic.
Why SRE Teams Are Adopting AI Right Now
Quick Answer: SRE teams are adopting AI because system complexity and alert volume now outpace what humans can reliably triage in real time.
Most teams do not adopt AI because it feels modern; they adopt it because queues are backing up. It is similar to airport traffic control during peak weather: when the sky gets crowded, coordination quality becomes the bottleneck, not raw pilot skill. SRE teams face the same pattern as microservices proliferate, deployment frequency rises, and one customer issue can span six systems before anyone notices the shared failure point.
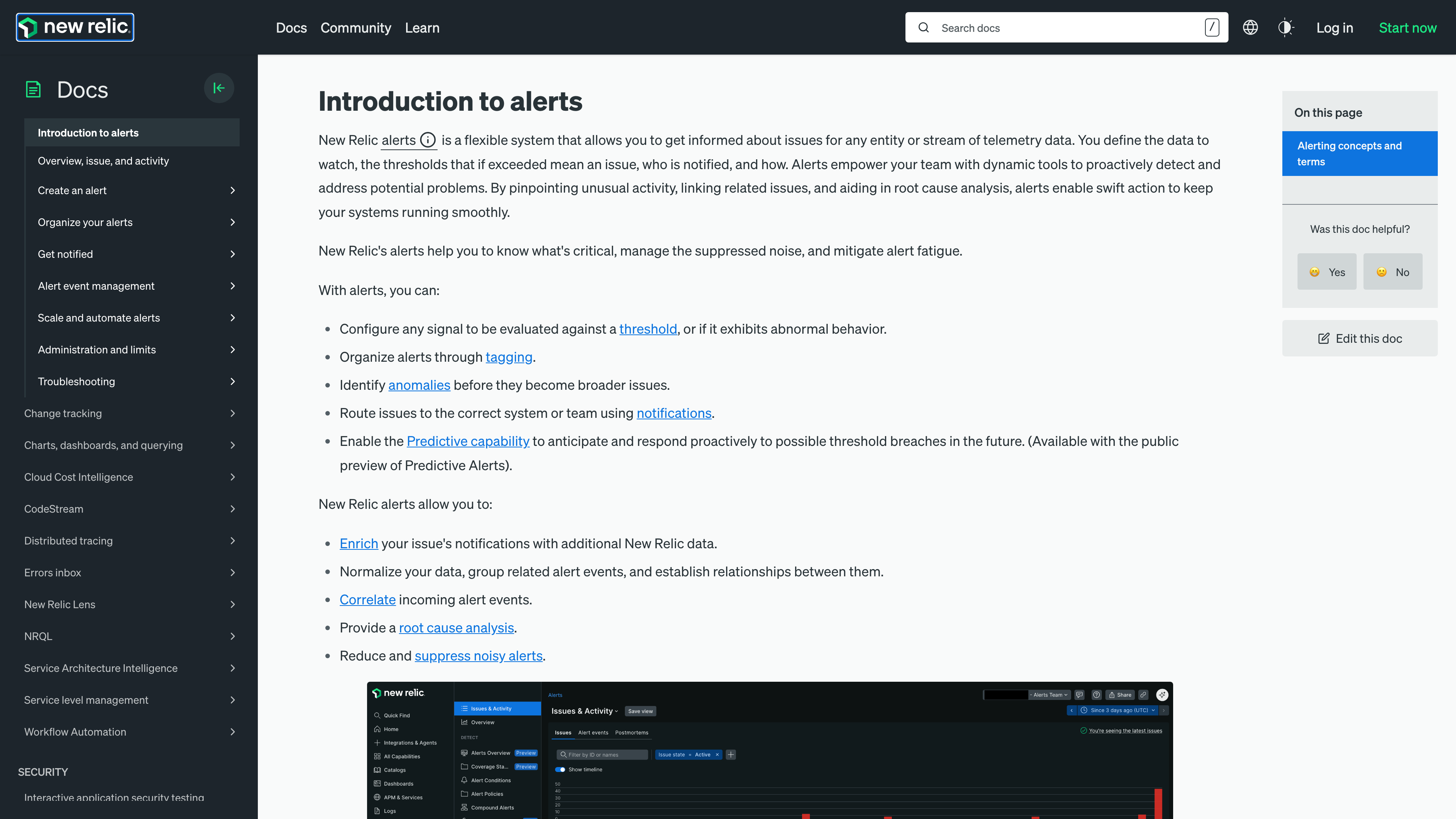
PagerDuty's incident lifecycle guidance and platform workflows from Datadog and New Relic all point to the same operational truth: detection is no longer the hard part, prioritization is. You can fire thousands of alerts per day and still miss the one sequence that predicts customer impact. AI-assisted triage reduces that gap by clustering related anomalies and estimating probable blast radius, which lets on-call engineers choose the highest-value intervention first.
What should your team do this week? Run a one-week shadow mode pilot where AI suggests priorities but does not auto-remediate. Compare results against human triage on three metrics: minutes to identify customer impact, duplicate alerts per incident, and escalation churn. If shadow mode does not beat your current baseline by at least 20 percent on one metric, pause deployment and rework your signal quality before expanding scope.
| Adoption Trigger | Old Manual Response | AI-Assisted Response |
|---|---|---|
| Alert flood during peak traffic | Pager manually groups alerts | Model clusters events and drafts one incident summary |
| Cross-service latency regression | Multiple teams investigate in parallel | Single timeline links deploy, trace spike, and dependency error |
| Nighttime on-call handoff | Context rebuilt from scratch | Shift summary generated with unresolved risk markers |
Incident Summarization and Root Cause Analysis Workflows
Quick Answer: The highest-leverage workflow is alert ingestion to AI timeline to human-verified root cause analysis, all inside a strict evidence chain.
A reliable incident workflow is less like brainstorming and more like air crash investigation: sequence matters, evidence quality matters, and every claim must be traceable. In production teams, the workflow that consistently works is: ingest events, build a timeline, propose hypotheses, test against telemetry, and only then issue a remediation recommendation. AI accelerates the first three steps, but humans still own the final two because false certainty is expensive.
Here is a concrete example from a payment API (Application Programming Interface) team that processed around 22 million requests per day. Their pre-AI median time to identify root cause during high-severity incidents was 41 minutes. After adding timeline synthesis from traces and deployment metadata, median identification dropped to 18 minutes over a six-week window, while false escalations dropped from 14 per week to 6. The key was not model size; it was forcing every AI claim to reference a metric spike, log signature, or release change.
Use this step sequence in your next incident drill:
- Collect the first 15 minutes of traces and logs, and mark user-visible symptoms.
- Ask the model for a timestamped summary with no fixes yet, only observed evidence.
- Request top three hypotheses and require one confidence reason per hypothesis.
- Validate the top hypothesis against service-level objective dashboards and recent deploy diff.
- Only after validation, let AI draft rollback or patch steps for engineer approval.
If you skip hypothesis validation, AI becomes a confident narrator instead of a reliable assistant. That is the technical gotcha most teams discover late. The practical fix is simple: add a policy that any remediation recommendation without attached telemetry references is automatically rejected in your incident channel bot.
Runbook Generation, Alert Noise Reduction, and Prioritization
Quick Answer: AI is most effective when it converts repetitive operational decisions into reusable runbooks and suppresses low-signal noise before people are paged.
Runbooks are like checklists in aviation: their power is not creativity, it is repeatability under stress. AI can draft runbooks quickly, but the quality jump happens when teams feed it successful incident patterns, rollback constraints, and dependency health checks from previous postmortems. That transforms a generic script into a procedure your team can trust at 3 a.m.
Alert noise reduction works the same way. Instead of deleting alerts blindly, let AI propose suppression windows, deduplication rules, and routing changes based on historical incident outcomes. When this is done well, on-call engineers see fewer but richer notifications that include probable impact, likely owner, and suggested first diagnostic command.
Use this practical checklist to deploy safely:
- Start with one incident class (for example, cache saturation) and generate only one approved runbook.
- Require a rollback path in every AI-generated runbook before it can be marked production-ready.
- Keep a human sign-off field so ownership stays explicit.
- Track false positive suppression monthly and reverse any rule that hides customer-impacting incidents.
| Automation Pattern | Primary Benefit | Failure Mode to Watch |
|---|---|---|
| Dynamic alert dedupe | Lower page fatigue | Over-aggregation hides separate incidents |
| AI runbook draft | Faster remediation onboarding | Unverified commands in critical paths |
| Priority scoring | Better triage order | Bias toward noisy services with more telemetry |
AI in CI/CD Pipelines and Deployment Guardrails
Quick Answer: In continuous integration and continuous delivery pipelines, AI should score deployment risk and surface review hints, not silently bypass release controls.
Deployment AI should behave like a sharp release manager, not an ungoverned autopilot. In a healthy pipeline, the model inspects pull request patterns, flaky test history, dependency updates, and change-scope volatility, then proposes a risk score with rationale. Engineers still choose whether to deploy, but they choose with better context and fewer blind spots.
CI/CD (continuous integration and continuous delivery) integrations in GitHub Actions and progressive delivery tools such as Argo CD make this practical: one AI comment can highlight that a supposedly small patch touches high-churn files and lacks rollback steps. That kind of intervention is useful because it catches operational risk before production rather than summarizing it after failure.
A good weekly workflow is to run AI risk scoring in advisory mode on all pull requests over two days, then enforce blocking mode only on services with user-facing service-level objectives. Pair that with one release retro where you compare predicted risk versus real incident outcomes. If predictions drift, retrain heuristics on recent data rather than adding more rules blindly.
Security guardrails also matter. The NIST AI Risk Management Framework and CISA secure-by-design guidance both reinforce a simple operating principle: if the model touches production pathways, you need traceability, policy boundaries, and override logs. That means storing prompts, outputs, and decision reasons in an audit trail alongside deployment metadata.
Metrics That Prove AI DevOps Impact
Quick Answer: Measure AI DevOps impact with reliability and delivery metrics together, so speed gains never hide stability regression.
If you only track velocity, AI will look better than it is. It is like judging a hospital by patient throughput without checking readmission rates. The right dashboard combines deployment speed with reliability outcomes, which is why teams often pair DORA (DevOps Research and Assessment) metrics with incident and error-budget views.
Start with four measurements for the first quarter: change failure rate, mean time to recovery, alert-to-acknowledgment latency, and runbook reuse rate. Then add one qualitative metric from postmortems: did the AI summary meaningfully reduce investigation handoff friction? That qualitative signal catches failure modes raw numbers miss.
A practical target matrix for the first 90 days looks like this:
| Metric | 90-Day Target | Decision Rule |
|---|---|---|
| Mean time to recovery | -25% | Keep AI triage only if outages resolve faster without extra false confidence |
| Change failure rate | No increase | Roll back AI risk scoring if failed deploys rise for two consecutive sprints |
| Alert-to-ack latency | -30% | Tune suppression rules if improvement stalls after week 4 |
Finish this section by assigning one owner for metric hygiene. Without ownership, teams collect numbers but do not make decisions. With ownership, AI operations stops being a side experiment and becomes part of your reliability engineering strategy.
Recommended Next Reads
Use these related guides to turn the workflow from this article into a team-level operating model.
aicourses.com Verdict
Quick Answer: These workflows produce the best outcomes when teams treat AI as a reliability and delivery multiplier, not a replacement for engineering judgment.
AI for DevOps works best when teams treat it as an operational co-pilot with strict evidence requirements. The productivity gains are real, but only when AI output is anchored to telemetry and runbook discipline.
If you are starting today, begin with one incident class, one service, and one shadow-mode experiment. Measure improvements against a clear baseline before scaling to the whole platform organization.
After that rollout, move to AI Developer Productivity Playbooks so you can connect operations gains with team-level delivery metrics. Want to learn more about AI? Download our aicourses.com app through this link and claim your free trial!
FAQ
Quick Answer: These are the questions teams typically ask when they move from experiments to production adoption and governance.
Should AI auto-remediate production incidents?
In most teams, no. Start with recommendation mode and add automation only after runbooks and safeguards prove stable.
How much data does AI need for incident triage?
Enough to build a timeline with logs, metrics, traces, and recent deploy context. Fragmented data sharply lowers reliability.
What is the fastest first use case?
Incident summary generation is usually the quickest win because it reduces handoff friction immediately.
Can small teams use AI SRE workflows too?
Yes. Smaller teams often benefit more because they have less specialized incident staffing.
Which metric should I track first?
Mean time to recovery is a strong starting metric because it captures direct operational impact.
How do I avoid over-trusting AI incident advice?
Require every recommendation to reference concrete telemetry and keep final approval with an on-call engineer.
Sources
The guidance above is grounded in primary documentation and engineering references:
SEO Metadata
Title: AI DevOps & SRE Automation for Developers
Meta Description: A practical guide to AI for DevOps and SRE automation, including incident workflows, runbook generation, CI/CD guardrails, and impact metrics.