Why Multi-Jurisdiction Compliance Is Hard
Quick Answer: The hard part is not collecting user data, it is proving that risk decisions satisfy different legal standards across markets while keeping onboarding usable.
Imagine running one rail network where each country uses different signaling rules: trains can move, but only if routing logic understands every jurisdiction at once. For stablecoin infrastructure, that means handling AML (Anti-Money Laundering), PEP (Politically Exposed Person), Travel Rule, and reporting requirements that vary by regulator and institution type. The EU MiCA regulation text and FinCEN's CDD rule show how documentation, monitoring, and beneficial-ownership expectations can differ by context.
Noah's Multi-Entity Challenge
Quick Answer: Noah needed one fast onboarding experience while maintaining different policy branches for licensed entities in the US, Canada, and Lithuania.
The analogy is a global ERP (enterprise resource planning) system with country-specific tax modules: one platform, localized policy behavior. In the Noah case study, the company describes using Sumsub workflows for licensed entities in Canada, the US, and Lithuania without building separate onboarding stacks. That decision reduced operational duplication while preserving market-specific control requirements.
Unified Yet Customizable Workflow Stack
Quick Answer: Noah's stack combined centralized orchestration with configurable, entity-aware rule logic for verification, screening, and monitoring.
Think of this as a policy engine sitting above payment rails: product teams keep a unified onboarding journey while compliance teams tune branch logic per license. The workflow model spans KYC (Know Your Customer), KYB (Know Your Business), liveness, sanctions screening, and transaction monitoring in one environment. Workflow Builder documentation reflects this configuration pattern directly.
If you want the conversion side of this architecture, pair this section with the onboarding-friction article. If you want the complete strategic context, return to the pillar guide.
Compliance Layer → Payment Orchestration → Settlement
Risk-Based Automation
Quick Answer: Risk-based automation adds checks when needed, so high-risk flows get enhanced scrutiny while low-risk flows move faster.
The closest analogy is airport security lanes with dynamic routing: some travelers move through standard checks, others are directed to deeper screening based on risk indicators. In practice, Noah's model combines profile risk scoring, anomaly detection, and triggers for enhanced due diligence. This aligns with the regulatory direction in both FINTRAC compliance guidance and Travel Rule enforcement expectations.
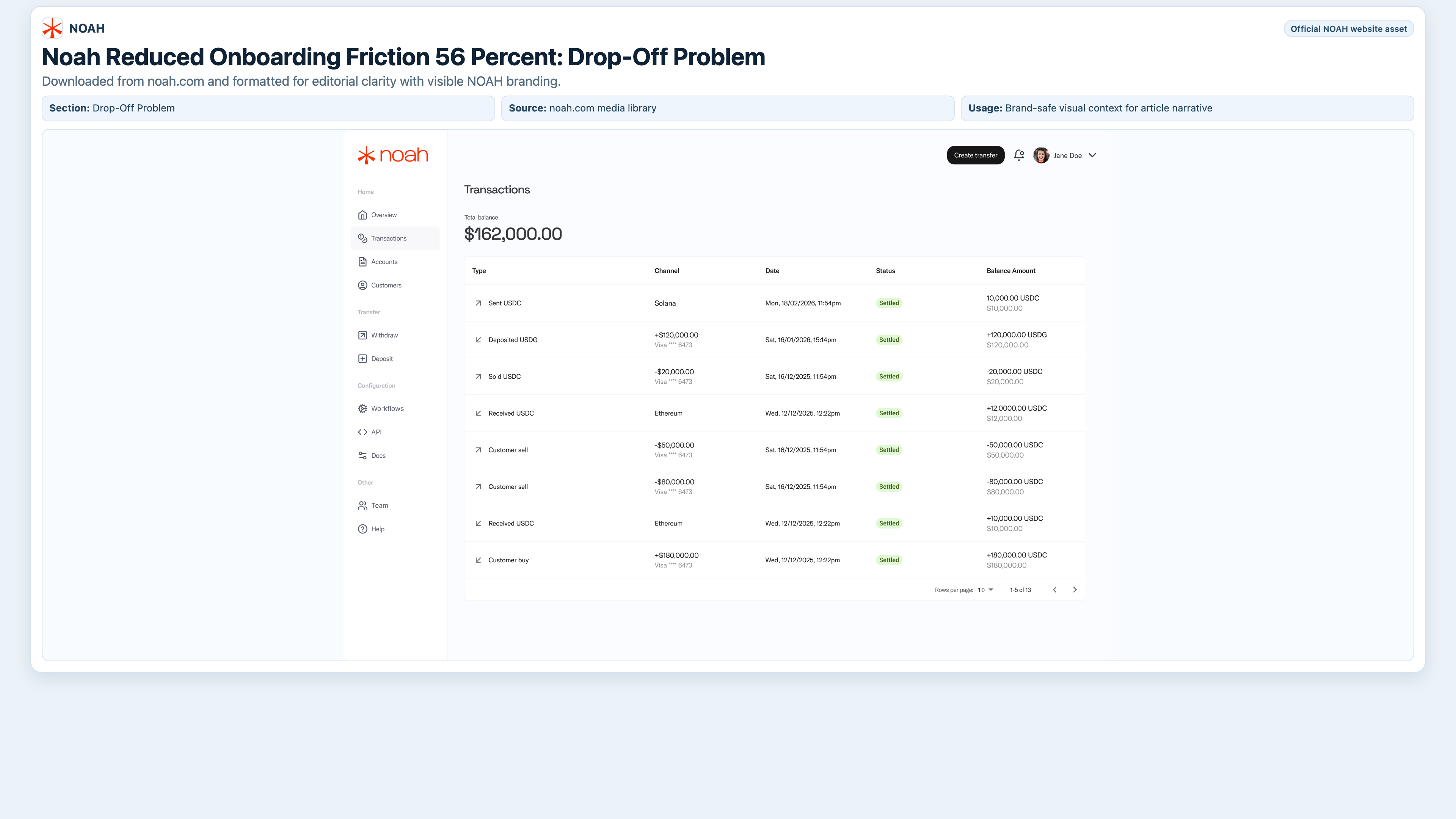
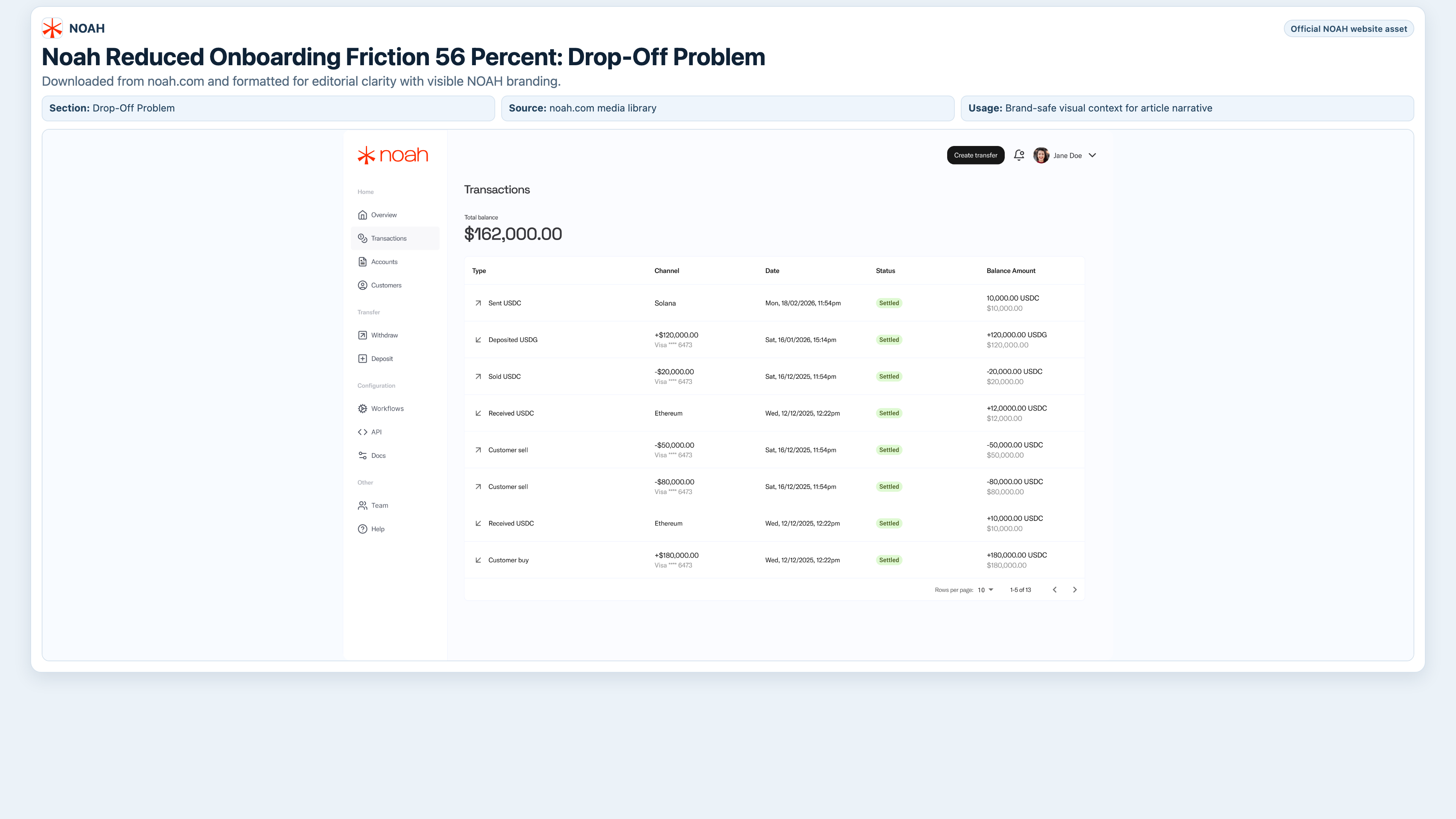
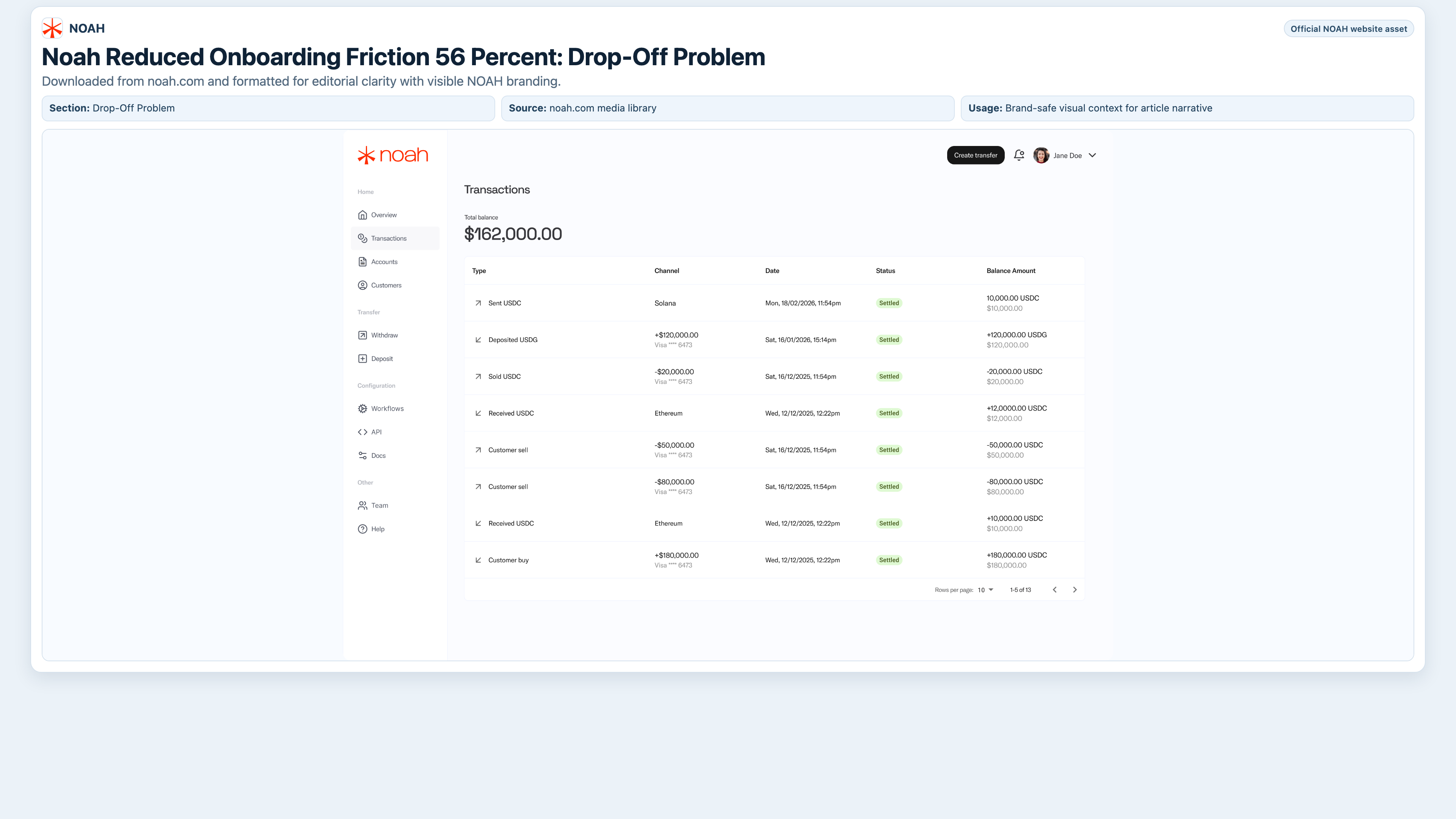
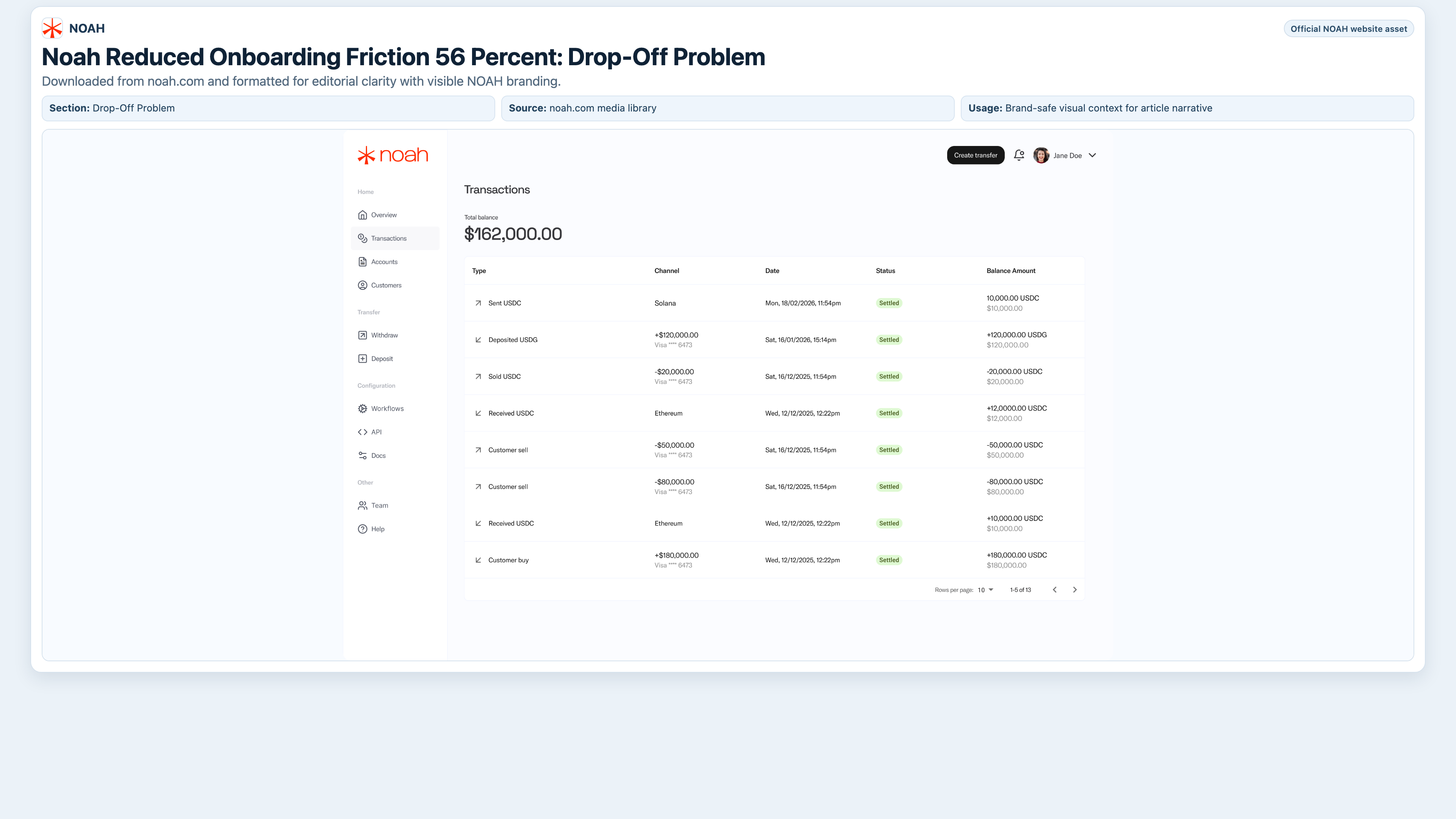
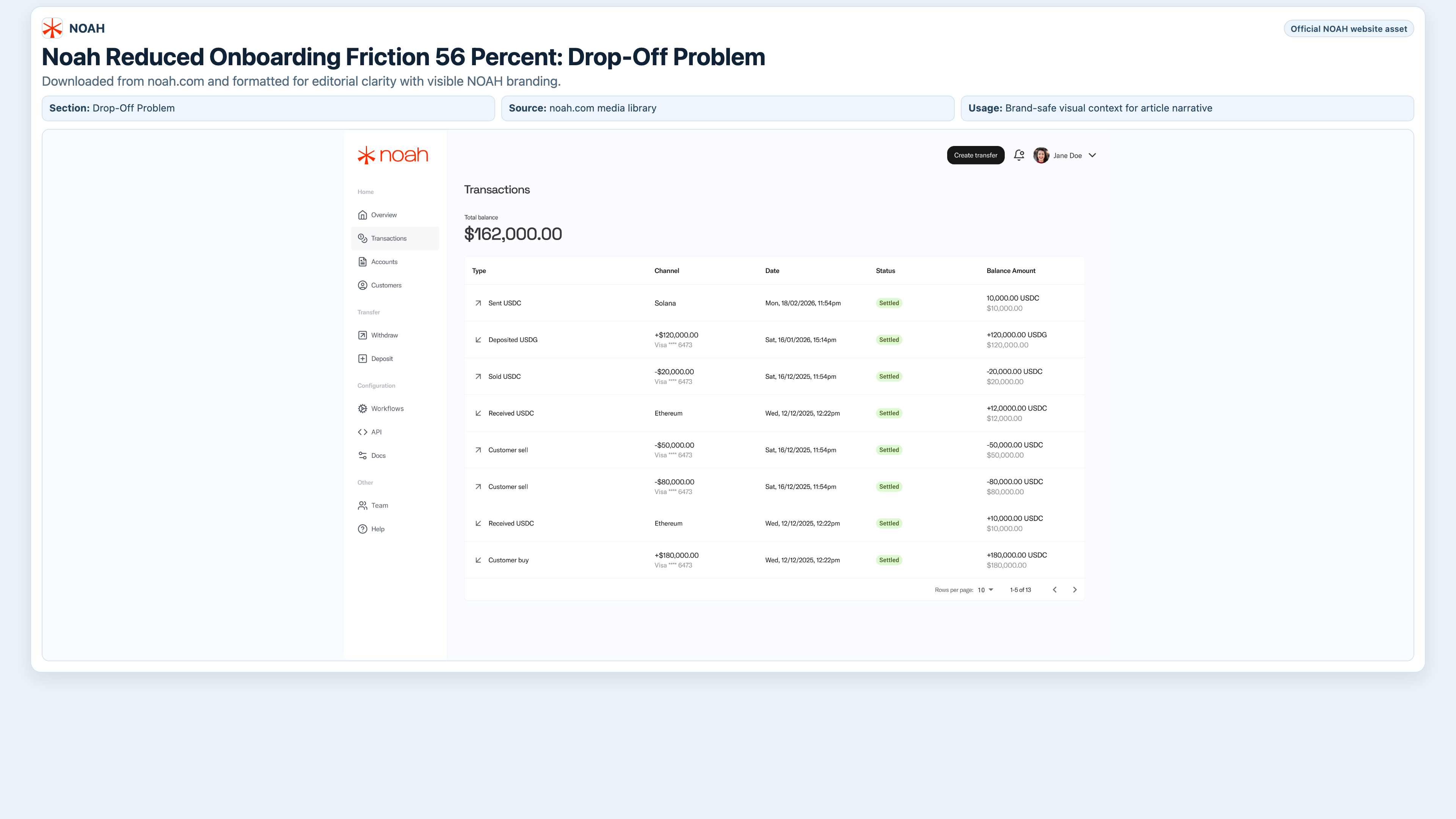
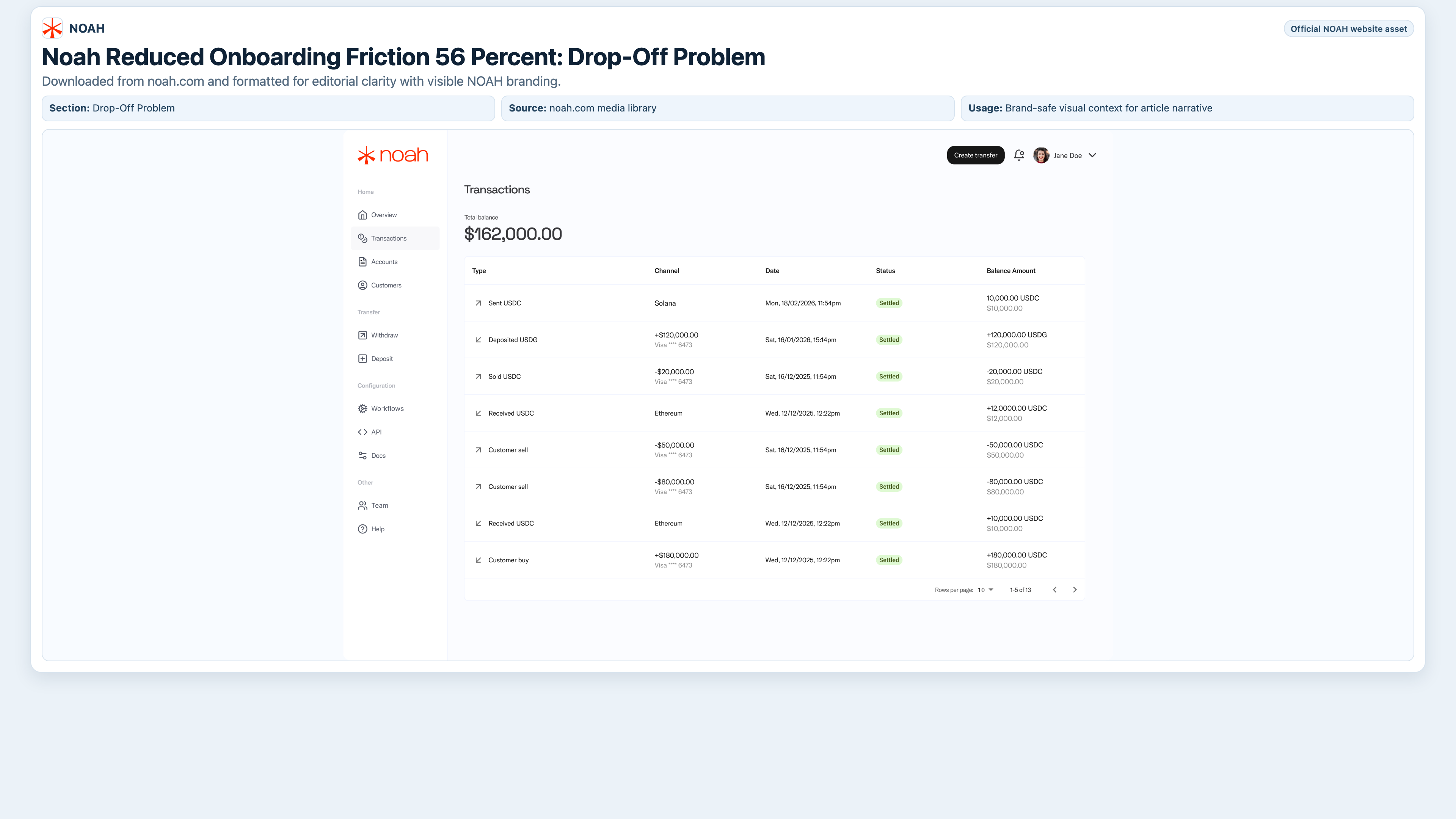
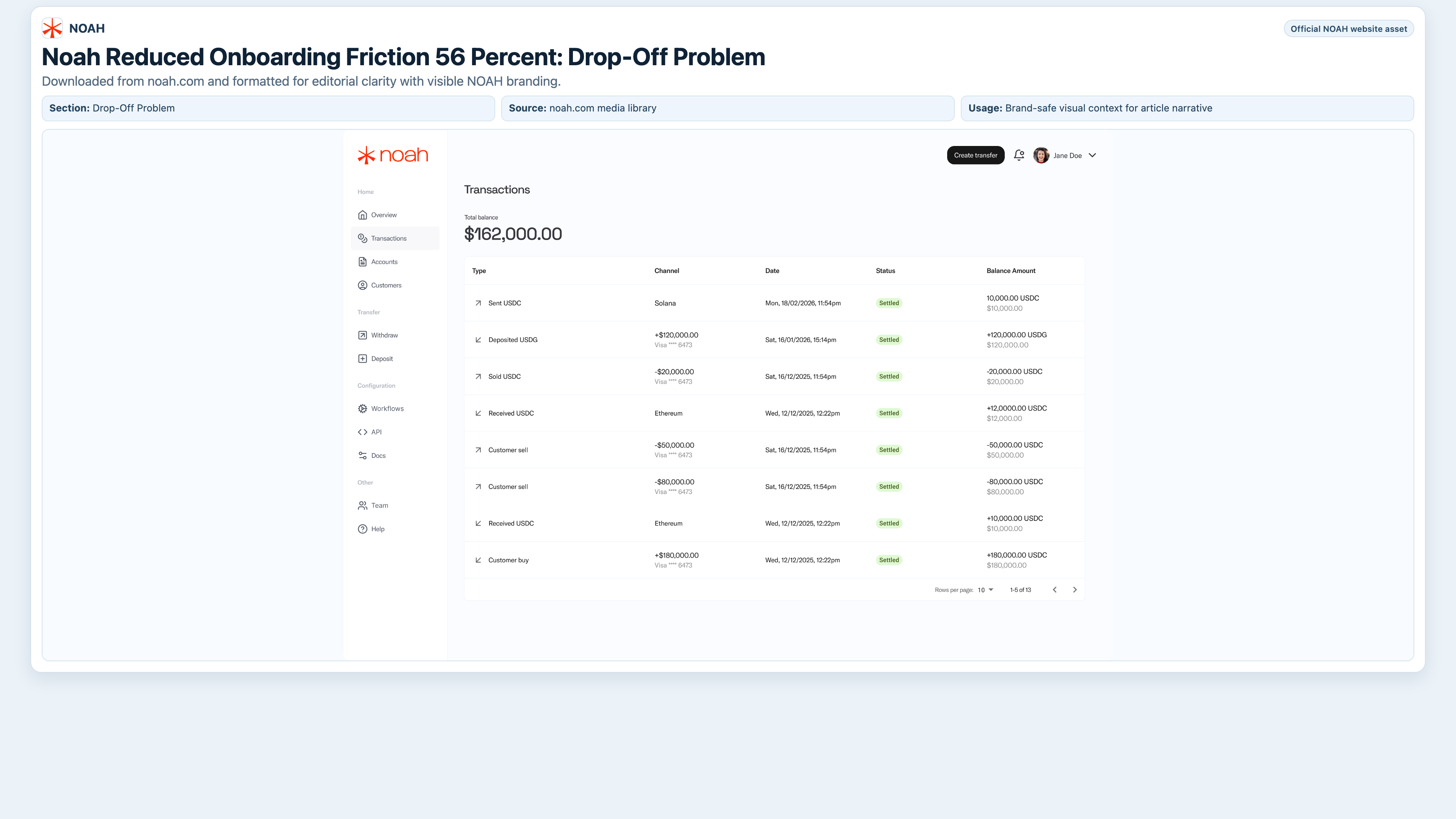
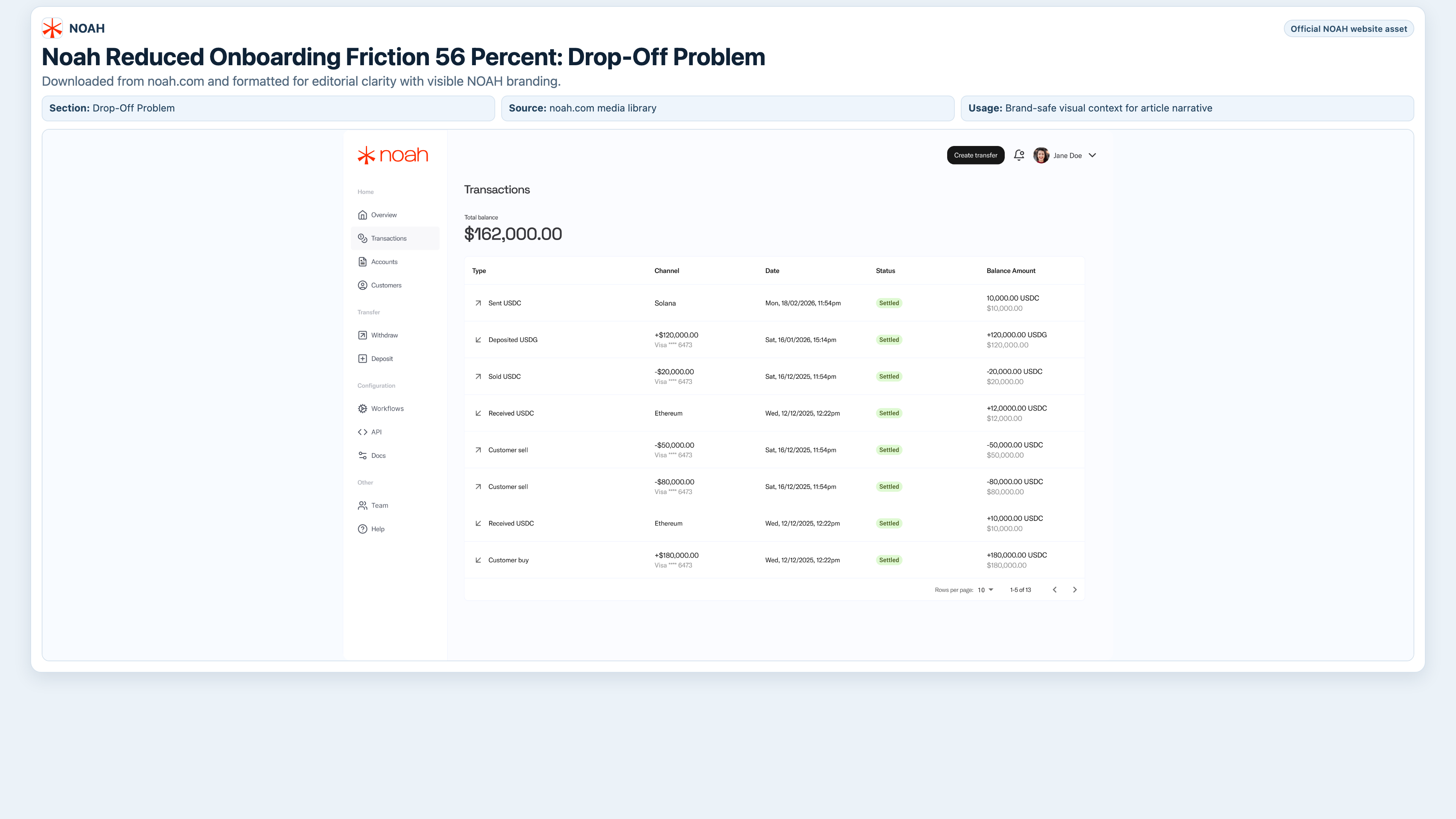
Metric Summary Box
- 56% drop-off reduction after workflow modernization
- 63% onboarding-time improvement (8.4 min to 3.1 min)
- 60% increase in auto-approval rates
- Document errors reduced from 18% to 7%
Auditability & Data Integrity
Quick Answer: Auditability is the architecture's proof layer: complete logs, screening history, and policy-version evidence that regulators can review without guesswork.
Picture a flight recorder in aviation: when something goes wrong, investigators need exact sequence, context, and system state. In compliance architecture, that means decision logs tied to the rule set that produced each outcome, plus immutable records of data used in those decisions. This is what makes controls defensible during supervisory review instead of relying on manual reconstruction.
| Before | After | Architecture Impact |
|---|---|---|
| Fragmented logs across tools | Unified event history | Faster audits and clearer root-cause analysis |
| Static one-size flows | Risk-based dynamic flows | Lower friction for low-risk users, stronger control for high-risk events |
| Manual policy interpretation | Entity-specific rule automation | Better consistency across jurisdictions |
Strategic Implications for Stablecoin Platforms
Quick Answer: A unified compliance architecture lowers marginal expansion cost and increases resilience when entering new jurisdictions.
The analogy is a modular factory line: once the base system is stable, adding a new product variant is cheaper than building a second factory. For stablecoin platforms, this means faster market entry, lower operational overhead per new entity, and better investor confidence in controls. It also reduces dependency on tribal knowledge because policy logic is codified and testable.
| Technical Requirement | Potential Risk | Learner's First Step |
|---|---|---|
| Entity-specific compliance templates | Policy mismatch in new markets | Build jurisdiction templates before onboarding launch |
| Travel Rule data propagation | Transfer interruptions and remediation backlog | Map required sender/beneficiary fields from onboarding to transfer payloads |
| Versioned policy logs | Weak regulatory defensibility | Store every decision with the policy version used at execution time |
Future Roadmap
Quick Answer: The next maturity step is dynamic, context-aware onboarding that combines reusable identity with live behavioral and transaction signals.
Think of this as adaptive cruise control for compliance: the system adjusts in real time based on traffic conditions rather than fixed speed rules. The Noah case-study roadmap language highlights dynamic risk flows, device signals, and transaction-pattern monitoring as future priorities. The objective is to keep fraud and financial-crime risk low while minimizing unnecessary friction for legitimate users.
This roadmap complements the conversion analysis in Article 2 and reinforces the strategic framing in the pillar article.
FAQ
Quick Answer: These are the implementation questions teams ask when moving from a single-market compliance stack to a global one.
Is one compliance stack enough for multiple jurisdictions?
Yes, if the stack supports entity-level rule customization and keeps jurisdiction-specific policy logic explicit and testable.
How do Travel Rule obligations affect architecture decisions?
Travel Rule obligations force data model alignment between onboarding and transaction systems. If those systems are disconnected, exceptions increase rapidly.
What is the first signal that architecture is failing at scale?
Manual override volume. When analysts repeatedly bypass default flows, it usually means policy logic is not aligned with real operating risk.
Do reusable profiles reduce regulatory scrutiny?
No. Reuse reduces repetitive user actions, but ongoing screening and monitoring still need to run according to local requirements.
Which article should we read first in this cluster?
Start with the pillar article, then read this architecture deep dive and the conversion analysis for implementation sequence.
aicourses.com Verdict
Quick Answer: Noah's architecture demonstrates that multi-market compliance scale comes from orchestration quality, not from multiplying disconnected tools.
Our view is that the technical moat here is policy orchestration discipline. Teams that encode entity-level requirements into one auditable system move faster than teams that duplicate onboarding stacks by market.
To apply this approach, map your existing decision points to jurisdictions, remove silent manual dependencies, and version your policy logic before expansion. That sequence will improve both regulatory confidence and operational speed.
Want to learn more about AI? Download our aicourses.com app through this link and claim your free trial!
Sources
- Sumsub: Noah x Sumsub case study
- Sumsub: Workflow Builder
- Sumsub: Travel Rule overview
- FATF guidance for virtual assets and VASPs
- EUR-Lex: MiCA Regulation (EU) 2023/1114
- FinCEN: Customer Due Diligence Final Rule
- FINTRAC: Compliance program requirements
- FINTRAC: Travel Rule guidance for EFT and virtual currency transfers